The Complete Guide to Strong Customer Authentication (SCA)
Last editedMar 20224 min read
Get all the key information about SCA, as well as when and were it will apply.
The background to PSD2 and SCA
The PSD2 is the 2nd EU Payments Service Directive.
The directive builds on three key areas of legislation first brought in with the original 2007 Directive. These areas include increased consumer rights in payments, creating a level playing field by bringing into scope the regulation of third-party access to account information and enhanced security.
Enhanced security refers specifically to a set of requirements called Strong Customer Authentication (SCA). These requirements have far-reaching implications for any business with an online presence.
This guide will explore SCA, who and what it affects and how businesses can prepare for the requirements taking effect.
What is Strong Customer Authentication (SCA)?
Strong Customer Authentication is a set of upcoming regulatory requirements, designed to make paying online more secure and, consequently, reduce payment fraud.
SCA adds an extra layer of security when end-customers make a payment online. Until now, shoppers have been able to simply enter their payment details and complete their purchase (although some businesses voluntarily choose to ask for further authentication).
How does SCA work?
SCA is a form of two-factor authentication designed to prove that end-customers are who they say they are, with specific rules around what constitutes ‘authentication’.
It requires two forms of validation out of three available categories.
What constitutes a method of authentication?
There are three valid categories of authentication available as part of SCA. Within each category, there are a number of potential methods for satisfying that category.
The three categories are:
Knowledge (something only the payer knows) - examples include a password, PIN, passphrase or secret fact/answer
Possession (something only the payer possesses) - examples include their mobile phone, smart watch, smart card or a token
Inherence (something the payer is) - examples include a fingerprint, facial recognition, voice patterns, DNA signature and iris format
Only when the payer has been able to provide two of these forms of authentication, will they be allowed to complete their payment.
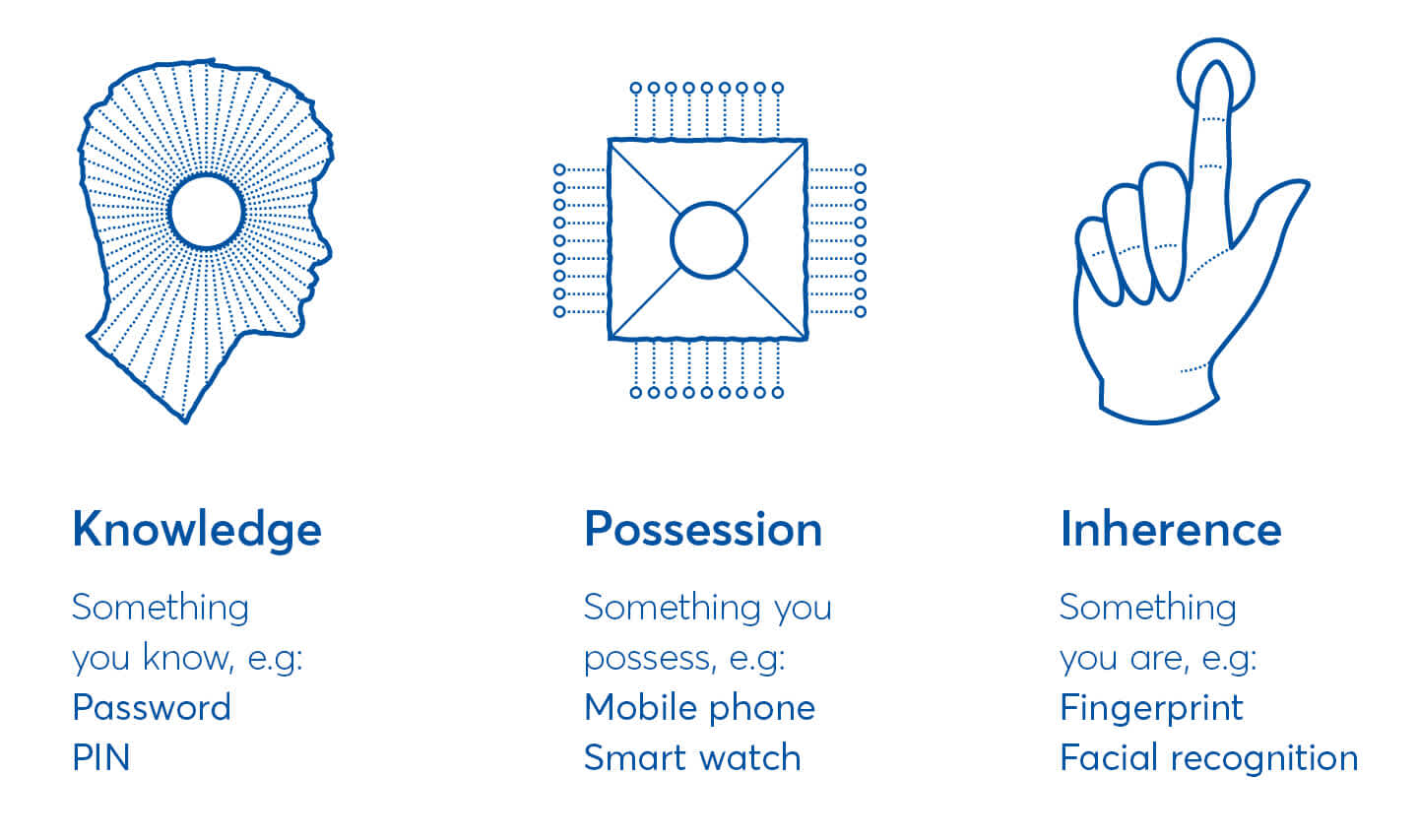
The three types of authentication allowed under SCA
On 21 June 2019, the EBA released a new opinion on what may constitute a compliant element in each of the three possible categories of inherence, possession and knowledge, as well as additional requirements on dynamic linking and the independence of elements.
What transactions does SCA apply to?
SCA is being brought in to make dealing with money and making payments online more secure and to reduce payment fraud. At a high level, SCA will be required where a payer transfers funds or access their account information.
In particular, SCA will apply each time a payer:
accesses its payment account online
initiates an electronic payment transaction
carries out any action through a remote channel which may imply a risk of payment fraud or other abuse
The main impact is very likely to be on card payments and bank transfers. The reason for this being that card payments are instant and initiated by the end-customer, and the payment or the consent to access account details is instant, which creates risk.
Does SCA apply to recurring payments?
Where payments are initiated by an end customer, SCA will only apply to the first payment in a set of recurring payments for the same amount. However, if the amount changes, then SCA will apply.
Where payments are initiated by the merchant receiving the funds, SCA will typically (although not in the case of standard Direct Debits) be required for the first payment in a series of recurring payments. So long as the subsequent payments are initiated by the merchant, further SCA will not be required so long as the amounts being charged are within the reasonable expectation of the end customer.
This means subscription businesses, SaaS businesses and membership businesses will all need to prepare for SCA.
There are, however, multiple exemptions to SCA, and certain out of scope transactions that will benefit businesses with recurring revenue.
Why is SCA coming into force?
SCA is part of PSD2. One of the aims of PSD2 is to provide protection for consumers.
Since the implementation of the original PSD, there have been new technological advances within the payments market seeing an increase of Third Party Providers (TPPs). These TPPs offer new and innovative ways of accessing consumers’ account information and initiating payments.
However, opening up access to consumer accounts in this way creates increased security risk, and the tradeoff is strict regulation on how TPPs and payment service providers get access to these accounts.
That’s where SCA comes in. It aims to ensure that the end customer is the rightful owner of the bank account or other payment mechanism (e.g. card). By going through a two-factor authentication process, the risk of fraud is perceived to be reduced.
In short, SCA is aimed at improving the security of payers’ online transactions and reducing payer fraud.
The cost of payments fraud
SCA is designed to reduce fraud during online transactions, but how much impact will it make?
The European Central Bank calculated the total value of fraudulent transactions using cards issued within SEPA and acquired worldwide amounted to €1.87 billion in 2019. 80% of which was accounted for by card-not-present transactions including, payments via internet, mail or phone.
According to Retail Dive, retailers worldwide could be set to lose $130 billion between 2019 and 2023 if significant measures aren’t taken to prevent card-not-present fraud.
In the UK alone, 40% of total fraud loss was down to card payments, more than any other payment method, in 2019.
Any reduction in the rate of fraud could result in a significant saving.
What countries will SCA apply to?
SCA (as part of PSD2) is a European-wide requirement and will be required for any applicable transaction where both the business’ payment service provider and the payer’s bank or card provider are located within the European Economic Area (EEA). If one of these is outside Europe, the requirement is for the payment service provider in Europe to use ��‘best efforts’ to apply SCA.
This means that even if a business is headquartered outside the EEA, if they take online payments from payers in the EEA, those transactions may still be subject to SCA.
It is highly likely that SCA will continue to apply to the UK, regardless of the outcome or timing of Brexit; the FCA has made its plans clear - it wants SCA to continue to apply; there has been no suggestion to the contrary by other European regulators.
The European Banking Authority's role in SCA
The European Banking Authority (EBA) is an independent EU Authority which works to ensure effective and consistent prudential regulation and supervision across the European banking sector. Its overall objectives are to maintain financial stability in the EU and to safeguard the integrity, efficiency and orderly functioning of the banking sector.
The EBA has released Regulatory Technical Standards (RTS) that outline the full remit of SCA for the EEA.
However, competent authorities from individual EEA countries, such as the FCA in the UK or BaFin in Germany will be responsible for enforcing SCA when it comes into force.
When does SCA come into force?
SCA regulations came into force on March 14th 2022. All e-commerce transactions should now be fully SCA compliant and firms should continue to take robust action to reduce the risk of fraud.
(Note: The FCA issued a further 6 month extension from the 14 September 2021 deadline to ensure minimal disruption to merchants and consumers, recognising the ongoing challenges facing the industry to be ready.)
This means that some PSPs may be allowed a delayed roll out, otherwise known as an ‘operational readiness’ period, during which the FCA and other regulators may not take enforcement action.
Security vs. convenience in the payment experience
What matters most to online shoppers?